- September 11, 2008
What is Antivirus Security?
Antivirus Security is a a new variant of the widely spread rogue anti-antispyware programs named Internet Antivirus and Antivirus 2009. Antivirus Security is advertised via malware and through the use of false and misleading pop-ups on web sites. If you are infected with malware that advertises this software, you will be presented with fake security alerts stating that your computer is infected and that you should download and install Antivirus Security in order to fix these problems. Web sites, on the other hand, will pretend to be online anti-malware scanners that are finding malware on your computer and stating you should download Antivirus Security to protect yourself. Both methods, though, have one ultimate goal; to have you download and install the software.
If you decide to download and run the software, Antivirus Security will scan your computer and list a variety of security risks that cannot be removed unless you first purchase the software. The program will also install a Windows Control Panel file that appears as an icon labeled Protection Center in your Control Panel. This Protection Center is a fake Windows Security Center that states you have no Antivirus protection and then will contain links back to the Antivirus Security homepage so you can download and install the software. Notice, that I said will in the previous statement. That is because the sloppy programmers forgot to replace the links in the Protection center so that they go to the correct site. Instead, all of the links go to the Antivirus 2009 home page instead of the Antivirus Security homepage.
This guide will walk you through removing the AntivirusSecurity program and its associated malware for free.
Fake or rogue antivirus software is a type of malware that pretends to have found an infection on the victim’s computer. In some cases, the cybercriminal’s objective may only be to scare the victim. However, many rogue antivirus programs also try to extract payment – for the removal of malware that hasn’t actually been detected… and may not even exist.
Avoiding rogue antivirus programs
Here are some useful tips – from Kaspersky Lab’s team of Internet security experts – to help you prevent rogue antivirus programs being downloaded onto your computer:
- Eliminate vulnerabilities – by keeping your OS and applications updated
Apply the latest security patches to your operating system (OS) and all applications, including:- Web Browsers
- Flash Player
- PDF reader… and all other applications that are on your computer
- Maintain your anti-malware defences
Keep your antivirus and Internet security software up to date . It’s a good idea to select the ‘receive automatic updates’ option within your security product. - Be cautious about search engine results
Avoid clicking on the sponsored links that feature within Internet search results. Sometimes it’s also advisable to be wary of the top search results. - Type the URL into the address bar
Whenever possible, try to access a website directly – by typing the URL into your browser. It may take a little more time – than clicking on a link that’s been generated by a search engine – but it can be a lot safer. - Beware of web surfing dangers
Avoid surfing unknown websites – especially social networks. - Don’t open unexpected attachments
If you receive an email attachment that you weren’t expecting, it might be dangerous. Don’t open an unknown attachment – unless you can verify that it is genuine and that it doesn’t contain any malware. - Think about that link… before you click it
Don’t click on random links in emails or instant messaging (IM) – or links on social networking sites.
Other articles and links related to malware and security
Rogue Antivirus Software
Fake or rogue antivirus software is a type of malware that pretends to have found an infection on the victim’s computer. In some cases, the cybercriminal’s objective may only be to scare the victim. However, many rogue antivirus programs also try to extract payment.
The worst type of virus is known as Crimeware, it is a type of malware that disguise as a genuine antivirus that will always alert you about discovering potential treat, due to the fake treat, your computer is now locked down for your own safety, and the only way to ‘unlock’ your computer is to pay a small ‘unlocking’ fee.
What you need is a very good standalone antivirus that detects and cleanses your system of the virus. There are plenty of standalone antiviruses, but some only do the job of detecting, while others require a small fee to perform the task. Two heads is better than one, without further ado, here are 5 free standalone antiviruses that detect and remove these fake antiviruses. Since they are free, just try all of them, even after the said virus is removed.
IMPORTANT! For these standalone antivirus to work, you need to disable ‘Windows System Restore’. By not disabling this feature, the virus will re-infect your system after the standalone antivirus removed it.
↓ 01 – McAfee Stinger
Stinger by Intel Security is a stand-alone utility used to detect and remove specific viruses. It is not a substitute for full anti-virus protection, but rather a tool to assist administrators and users when dealing with an infected system. Stinger utilizes next generation scan engine technology, including process scanning, digitally signed DAT files, and scan performance optimizations.
The new Stinger by McAfee has been developed to specifically target “FakeAlert” threats being seen in the wild. It is probably the only tool in the market that has the ability to remove all the strings and files by a fake antivirus. If you happened to have the following antivirus on your system, chances are, and your system is infected with these ‘fake’ antivirus (virus or Trojan)
↓ 02 – Norton Power Eraser
Norton Power Eraser is specially designed to aggressively target scam-ware. It uses our most thorough scanning technology to eliminate threats that traditional virus scanning doesn’t always detect, so you can get your PC back.
Because Norton Power Eraser uses aggressive methods to detect threats, there is a risk that it can select some legitimate programs for removal. If you accidentally remove a legitimate program, you can run Norton Power Eraser to review past repair sessions and undo them.
↓ 03 – Malwarebytes Chameleon
Note: The Chameleon engine is bundled into Malwarebytes Anti-Malware as shown in the screenshot above. Malwarebytes Chameleon technologies gets Malwarebytes Anti-Malware installed and running when blocked by malicious programs. It is a command-line utility, yet this does not imply it should only be used by tech-savvy ones as no user input is required once the tool is launched, as all the actions are initiated automatically.
Malwarebytes Chameleon per se cannot clean any computer of trojans or viruses, it can prove to be a vital tool when one’s PC is infected and they can no longer rely on their antivirus solution to eradicate the problem. It automatically downloads, installs and runs a renowned security product, namely Malwarebytes Anti-Malware, so as to clean the detected infection.
↓ 04 – Kaspersky Virus Removal Tool
Designed to remove different types of infections from your PC. It’s easy to use and compatible with all antivirus products. Kaspersky’s tool on the other hand has taken some protective measures: it can be installed on infected computers, even in Safe Mode, and it can automatically remove viruses, Trojans, rootkits, adware or spyware.
↓ 05 – TrendMicro Anti-Threat Toolkit
Fake Antivirus (FakeAV) threats have been rampant in the past few years. Various FAKEAV variants have infected millions of PCs and are continuously spreading worldwide.
One reason why FAKEAV infections have become well-known to users is because they have visual payloads. Variants of the malware family often display pop-up messages telling users that their machines have been infected. This may cause panic among users, pressuring them to purchase rogue antivirus applications in the hope of resolving the issue. Users, however, should never purchase antivirus software from unknown sources.
– 2021-04-06 Also known as AntivirusLive | Type: Rogue Antispyware
Antivirus Live Removal Guide
- Antivirus Live – a fake anti-malware app that should be eliminated as soon as possible
- Malware infection can be not noticed initially
- Remove Antivirus Live by using legitimate security tool
- How to prevent from getting rogue antispyware
What is Antivirus Live?
Antivirus Live – a fake anti-malware app that should be eliminated as soon as possible
Malware creates fake entries in order to make users believe that their computers need fixing
Antivirus Live is a rogue security application, a fake malware removal tool that enters a computer with the help of Trojans and other malicious software. It is from the same family as Antivirus System PRO and Spyware Protect 2009. Once installed, AntivirusLive will display fake security alerts and notifications about serious computer security threats or infections.
The rogue application will also block almost all programs, especially anti-virus, to protect itself from being deleted. You will see the “Application can not be executed” warning when you launch applications. To make things even more complicated, it will hijack Internet Explorer and change LAN Settings. Antivirus Live enables proxy servers for LAN and blocks security-related and antivirus software websites.
| Name | AntivirusLive |
| Type | Malware, rogue anti-spyware |
| Distribution | Social engineering campaigns, Trojans |
| Elimination | Follow the instructions below and scan the infected device with a legitimate anti-malware |
| System fix | If you noticed that your Windows system was damaged, fix it with an automatic solution Reimage Intego |
Malicious program will state that your computer is badly infected with Trojans, worms, spyware, and other malware. Then it will ask you to pay for a full version of the program to remove the infections which do not even exist.
The main goal of rogue antivirus app is to trick you into purchasing the program. In order to achieve its goals, the misleading application will simulate a system scan and report false scan results. In other words, this is nothing more but a scam. Do not purchase it!
What is more, this bogus security tool will impersonate Windows Security Center and state that Windows did not find any anti-virus software on your computer and that Windows is not updated. Obviously, the rogue program will suggest you to activate the app in order to protect your computer.
And that’s, by the way, the main difference between legitimate Security and fake ones. The legitimate one does not promote any particular anti-virus software. When this fake anti-spyware application is running, you will also see many fake security alerts. Some of them will state:
Windows Security Alert
Windows reports that the computer is infected. Antivirus software helps to protect your computer against viruses and other security threats. Click here for the scan of your computer. Your system might be at risk now.
Infiltration alert
Your computer is being attacked by an Internet Virus. It could be a password-stealing attack, a trojan-dropper, or similar. Threat: Wind32/Nuqel.E
To eliminate this malware, you would have to initiate a scan with a powerful security tool – we recommend using SpyHunter 5 Combo Cleaner . After all the malicious files are gone, you should also clean your browsers and fix damaged system files. Since this process might take a while and be a bit complicated for regular computer users, we advise performing these steps automatically with Reimage Intego .
Malware infection can be not noticed initially
Antivirus Live is promoted through Trojans’ use that comes from fake online scanners and other misleading websites. It is also distributed using social engineering. This means that users are presented with fake claims online, only to be taken advantage of. For example, a pop-up ad might say that your computer is infected (and look similar to how Microsoft error alerts look like) or that your software is out of date and needs to be updated urgently. All these are tricks that make users install malware without realizing it.
Therefore, in order to avoid being tricked, follow these tips provided by security experts:
- Install a robust anti-malware and always keep it updated;
- Never postpone Windows updates and install security patches for all software;
- Install ad-block to avoid malicious ads and scripts;
- Do not believe claims that something is missing from your system, or that it is infected with a virus.
- Use strong passwords for all your accounts and never repeat them.
Remove Antivirus Live by using legitimate security tool
As you can see, Antivirus Live is a totally useless and even dangerous application. Before you can remove this infection, you have to end all processes associated with malware. Otherwise, you won’t be able to run any anti-spyware/virus software. First of all, you have to disable the proxy server for LAN in Internet Explorer or use another browser, for example, Firefox or Opera.
How to disable a Proxy server for LAN in Internet Explorer:
- Open Internet Explorer. Click on the Tools menu and then select Internet Options.
- In the Internet Options window, click on the Connections tab. Then click on the LAN settings button.
- Now you will see the Local Area Network (LAN) settings window. Uncheck the checkbox labeled Use a proxy server for your LAN under the Proxy Server section and press OK.
Now terminate malicious processes. It should be [random]sysguard.exe, for example, wmcqsysguard.exe.
Do not reboot your computer after using Process Explorer and terminating all related processes. Now you should be able to download an automatic Antivirus Live removal tool or another anti-spyware application.
Most importantly, do not purchase this malicious app. If you have already done that, please contact your credit card company and dispute the charges.
In essence, this is a copy of the Total Security rogue program, and it’s not too hard to remove
- Instructions for removing the fake Win 7 Anti-Spyware 2011 software
- Instructions to remove the fake Desktop Security 2010 application
Essentially, this is a copy of the Total Security rogue program, and it’s not too hard to remove . The purpose of counterfeit software is phishing, causing users to believe in bogus warnings about the status, the number of viruses, spyware, malware . in their computers. If you look closely, you will see that it has the same interface as Total Security, only slightly different in the trace file. When operating in the background, the program will display an interface similar to the default application of Windows Security. When the user clicks on the icon, the program will immediately display a very authentic Microsoft-style bulletin board and recommend that Cyber Security be updated. And then ask the user to buy the license to activate the program license. As they proceed to update the program, viruses, trojans and spyware will race to the user’s computer.
Some expressions of the computer have been infected with Cyber Security
– Always show serious results about the security situation of the computer
– Automatically activate scan mode when the system starts
– The warning icon always appears in the system tray
– Popup window and homepage address always point to fake application’s website
Some pictures of Cyber Security program
To overcome these symptoms, many security experts recommend that the community of users using Spyware Doctor with Antivirus.
Manual removal of Cyber Security
Turn on Task Manager, find and turn off the following processes: tsc.exe, csc.exe
Next, find the following keys in the Registry and delete all that are related to Cyber Security:
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionCyber Security
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun ‘csc.exe’
And delete all executable files * .exe in % Program FilesCS folder : iehelpmod.dll, csc.exe, iehelpmod.dll (this file is located in c: windowssystem32 folder), winsource.dll, Help.lnk, Registration.lnk and Cyber Security.lnk.
If you do all the steps above without any problems, it means that you have successfully removed the Cyber Security rogue software from the system. To ensure the safety of the system, you can refer to the features and use the security programs of the following reputable firms: Spyware Doctor with Antivirus, Norton, Trend Micro, Kaspersky, AVG, MalwareBytes or other applications Available security tools of Meta company here.
Lowell is the founder and CEO of How-To Geek. He’s been running the show since creating the site back in 2006. Over the last decade, Lowell has personally written more than 1000 articles which have been viewed by over 250 million people. Prior to starting How-To Geek, Lowell spent 15 years working in IT doing consulting, cybersecurity, database management, and programming work. Read more.
You might be wondering why we have a screenshot of what appears to be AVG Anti-Virus, but is in fact a fake anti-virus malware that holds your computer hostage until you pay them. Here’s a really simple tip to defeating these types of malware, and a quick review of other options.
Not sure what we’re talking about? Be sure to check out our previous articles on cleaning up fake antivirus infections.
So what’s the problem? Can’t you just run a anti-virus scan? Well… it’s not quite that simple. What actually happens is that these pieces of malware block you from running almost anything on your PC, and often prevent you from running apps from a Flash drive, with an error like this:
Once you encounter this error, there’s a couple things you can do. The first one is almost stupidly simple, and works some of the time:
Move the Dialog, and Try Again!
Yeah, that’s right—reader Robert wrote in to tell us that you can often just move that error to the side of the screen, and then try to run your anti-malware or anti-spyware application again. Turns out that some of the errors will only run once… and then you can get your favorite application running.
If that doesn’t work, then here’s the next great tip…
Rename Your Anti-Malware App to Explorer.exe
Since most of the fake anti-virus malware needs you to be able to slightly use your PC, the one executable that it won’t ever block is “explorer.exe”, since they want you to be able to get online and go to their site and pay them—not so easy if you have no Start Menu.
So just rename your favorite anti-malware application to explorer.exe, and you should be able to use it.
Thanks to reader Jeffrey for writing in with this tip.
General Guide to Defeating Fake Anti-Virus Infections
There’s a couple of steps that you can generally follow to get rid of the majority of rogue antivirus infections, and actually most malware or spyware infections of any type. Here’s the quick steps:
- Try to use the free, portable version of SUPERAntiSpyware to remove the viruses.
- If that doesn’t work, reboot your PC into safe mode with networking (use F8 right before Windows starts to load)
- If that doesn’t work, and safe mode is blocked, try running ComboFix. Note that I’ve not yet had to resort to this, but some of our readers have.
- Install MalwareBytes and run it, doing a full system scan. (see our previous article on how to use it).
- Reboot your PC again, and run a full scan using your normal Antivirus application (we recommend Microsoft Security Essentials).
- At this point your PC is usually clean.
These steps generally work.
Can’t Even Boot Anymore? Here’s Your Solution
All you have to do is use a repair disk from one of the anti-virus manufacturers, who have each created downloadable ISO images that you can burn to a CD, or install onto a USB flash drive. Boot from it, run a scan, and then your PC will be clean.
We prefer using the BitDefender CD, since it’s automated and simple, but it couldn’t hurt to use more than one if necessary… so why not combine a bunch of recovery tools together? Here’s how:
4. Malwarebytes Antimalware and Chameleon
The Malwarebytes software is perhaps the most well known and popular software for removing just about all types of fake antivirus, fake hdd scanners, fake police ransom software and much more. The good thing about this program is it can remove and restore to normal most changes malware like this leaves behind such as bogus registry entries, alterations to the system settings such as file types or policies, and leftover files etc.
Malwarebytes Pro can protect your system from rogue software installing itself in the first place, but the free edition is an on-demand scanner only which can clean up the mess left behind after an infection. As such, you need to be able to get the free version installed after either killing the rogue process from another program that can terminate the process such as RogueKiller, RKill or Process Explorer for example.
Another option is using the Malwarebytes Chameleon tool which is designed to get the Antimalware application installed and running while any rogue or fake antivirus software is still active on the system and preventing a normal install. The zip contains differently named files which are actually the same file just with different extensions to help get around any block. The tool will attempt to kill any rogue processes, then automatically download, install and run a scan with Malwarebytes Antimalware. This method isn’t foolproof though and some rogues can still block the Chameleon tool from running such as the Smart/Internet Security fake antivirus when we tested it.
Malwarebytes Antimalware is a valuable program to cleanup the after effects of rogue or fake software and should also be run after tools like RogueKiller and RKill have been used to remove any remaining remnants and get your system back to normal.
5. Process Explorer
While it’s true Process Explorer is not a fake antivirus removal tool in itself, because most fake rogues disable Windows Task Manager so you can’t easily kill them, using a third party task manager tool such as this can help you quickly disable the rogue process allowing other tools like Malwarebytes to install and clean up the mess. Of course, if you prefer Process Hacker or a different tool, that can be used as well.
It’s quite likely that the Process Explorer executable you download (Procxp.exe) will not run as exe file launching probably has been disabled by the rogue program, renaming it to Winlogon.exe, Explorer.exe, Userinit.exe, Wininit.exe or Iexplore.exe will likely solve the problem. This is probably due to the fact that the fake program has to allow the real files with those names to run or windows won’t boot properly to the desktop allowing the fake nag messages to show. Finding the rogue process is usually quite easy as it often has an obscure or random character name and will be in the explorer.exe process tree. Then simply right click on it and select Kill Process. After that, you can install a Malware scanner or run your resident security software to clear the remains.
6. Remove Fake Antivirus
We thought the Remove Fake Antivirus software is worth a quick mention because you will sometimes see it recommended to remove a piece of fake antivirus software from various sources on the internet. Unfortunately, the program is out of date these days and quite ineffective against most rogueware produced in the last couple of years, not detecting the System Doctor 2014, System Care or Smart/Internet Security rogues we tried. It still might be capable of removing the problem if what’s infiltrated your machine isn’t brand new though.
Although the utility itself has limited usage, the Free of virus website that created it still has lots of useful and more recent information about how to manually remove newer fakes including those we mentioned in the previous paragraph.
Some Quick Tips to Help Remove Fake Rogues
Although the methods above should be more than enough to remove just about all fake antivirus or fake hdd scan software currently around, if you come up against a more aggressive rogue where they don’t work or still having issues removing the fake process, there are a few other things you can try to get around the problem:
These fake programs are nearly always user specific, meaning that it will only affect the user account that installed the rogue in the first place. If you have more than one account on the computer, simply switch to another user and it should be unaffected meaning you can install or run scanning software from there to remove the threat. You can also go to Control Panel and create a new account from an infected account if you’re the only user.
As they are mostly started by using the Run or RunOnce registry keys, you can easily bypass most rogues by simply booting into Safe Mode (F8). Third party applications that normally start with Windows are ignored while booting to Safe Mode and this includes the fake antivirus software meaning you can simply run a removal tool or manually remove the threat from there.
A simple tip if you’re a User account and not Administrator is to right click on the program you want to run such as RogueKiller or RKill and select “Run as Administrator”. This has an effect of elevating your privilege level above that of the the fake program so you can run the executable file.
Unless you’re an experienced power user who knows how to get by around computers, you need a security solution to secure your digital life. Your basic protection comes from an antivirus, and there are plenty of choices available. Some are free to use, while others require a paid subscription. Some work as a standalone program, while others are part of a security suite. And while some offer genuine protection, there are some that only pretend to be the real deal. Yes, fake antivirus does exist.
What Is a Fake or Rogue Antivirus?
Simply put, a fake antivirus is any software that looks like security software but functions otherwise. In most cases, fake antiviruses are malicious programs designed to manipulate users into spending money in exchange for cleaning a supposed computer infection. Fake antiviruses are related to the class of malware known as scareware.
What Are Some Examples of Fake Antivirus?
Oftentimes, rogue security software sounds generic and may use “antispyware,” “antivirus,” “defender,” “protection,” “security” and other related words as part of its name. Examples include Security Scan 2009, Internet Defender 2011 and System Tool 2011. Many rogue antiviruses are actually variations of one specific malware. Cybercriminals regularly alter the appearance and name of their malware to create new variants that are distinct enough from the ones already recognized by users and neutralized by legit security software.
Some fake antivirus disguise themselves as built-in tools of Windows and pretend to offer security updates from Microsoft. An example is Antivirus XP 2008, which may also go by a different name like Antivirus XP Pro, Windows Antivirus or System Care Antivirus.
How Do You Recognize a Fake Antivirus?
At first glance, a well-designed fake antivirus looks authentic. Its user interface or dashboard has many of the interface elements of a genuine antivirus: a status page that shows the security level of your computer, a section for your settings and updates, and buttons for scanning your computer. If you take a closer look, however, you may notice that some things are a bit off. For instance, you may find spelling and grammar errors in the texts. The user interface may show odd button placements and visual glitches.
Perhaps the biggest clue that an antivirus is fake is that it incessantly disrupts you from your normal activities by automatically initiating a “scan” without your approval. In addition, it frequently displays pop-up dialog boxes, warning messages and other distractions. Granted, some legit antiviruses (particularly the free ones) can be bothersome when sending you notifications and promotional offers, but fake antiviruses are even worse.
If you’re unsure, you can always look up your antivirus online and see if it’s legit or fake. You should be able to find genuine product pages for antiviruses from known security vendors. If you search for rogue software, on the other hand, you’ll likely find links to discussion forums and article guides that provide solutions on how to remove the rogue software.
How Does a Fake Antivirus Infect Your Computer?
If you look for security solutions online via search engines, you might stumble upon malicious URLs. Cybercriminals make use of search engine optimization so that their malicious websites that host fake antiviruses consistently rank higher in search results. Users who visit these websites risk getting a rogue antivirus as a drive-by download—a download that occurs without user awareness. The websites may also mislead users into believing that their systems have been compromised and convince them to download fake antivirus software directly. Cybercriminals also employ online advertising and phishing emails to spread their fake antivirus software.
Once the download is complete, the rogue software is capable of installing itself by exploiting existing vulnerabilities of different file formats, such as PDF, SWF and SQL.
What Does a Fake Antivirus Do?
The primary objective of a fake antivirus is to cause panic and tempt the victimized user to pay for services or purchase additional software. To accomplish this, the fake antivirus regularly feigns a virus scan and provides the user with a detailed report, which would claim that a huge number of viruses or pornographic files have been found in the computer. In addition, the fake antivirus may discreetly modify various settings of the operating system and the user’s programs, and later present these changes as problems. More cunning variants of fake antiviruses even mimic system crashes and the infamous blue screen of death to sow feelings of fear and anxiety to the user even further.
Like other pieces of malware, a fake antivirus may slow down your computer’s performance, add new desktop shortcuts, redirect you to adult sites and change the browser homepage. A fake antivirus anticipates the user eventually realizing that he has a malware infection, which is why it also alters systems settings to thwart any attempts of uninstallation.
How Do You Remove a Fake Antivirus?
Removal process may vary between variants of fake antiviruses. If your computer is infected, the general steps below can help remove the rogue programs.
First, run a full system scan using an updated antivirus, such as Windows Defender and Microsoft Safety Scanner. You may also use legit, standalone virus removal tools from third-party developers. Examples include RogueKiller by Tigzy and Malwarebytes Antimalware.
If the fake antivirus actively blocks your attempts to run your removal tools, use utilities like Process Explorer to terminate rogue processes first before trying again.
If the infection persists, restart your computer in Safe Mode with Networking, and repeat running a full system scan.
Open every Web browser installed in your computer and reset their settings.
How Can Your Protect Yourself From Further Fake Antivirus Infections?
If a website warns you that your computer is infected, ignore it and close the browser window or tab that’s showing the warning message. Remember, your antivirus do not need to use your Web browser to send you a warning, and a legitimate antivirus can only alert you about malware detections if it’s already installed on your computer. Do not visit websites with questionable reputation, as they’re more likely to show you fake virus warnings.
Install an updated antivirus and firewall. Having pop-up blocking software also helps you avoid unwanted pop-up messages.
Be skeptic of high pressure sale tactics that convince you to take action immediately and purchase products and services. Do not click on links or open email attachments without determining whether they’re clean or dangerous. If you need online help from your antivirus vendor, proceed directly to their official website and look for contact details there. Be cautious of links in search engine results, even if they rank high in search results.
Most of you know how important it is to have security software on your computers to stay protected from viruses, malware, spam, and other internet threats. Unfortunately, cybercriminals also know that it is critical to have a security solution, and they are using this knowledge to trick us into downloading fake virus protection that is designed to do harm to your computer.
Spotting a Fake Antivirus Solution
Fake antivirus software is one of the most persistent threats on the internet today. It masquerades as legitimate malware protection, but is actually a malicious software that extorts money from you to “fix” your computer. And often, this new antivirus program disables your legitimate security software that you already have, making it challenging to remove.
A rogue antivirus program will often hook you while you’re browsing the web by displaying a popup window claiming that your computer may be infected with various online threats. Often, the popup includes a phishing link to download security software that offers to solve the problem, or redirects you to a site that sells the fake antivirus application. It is also often also called scareware since the hackers use messages like “You have a virus,” as a way to get you to click on their message.
Because having an infected operating system usually means lost data, time, and money, most of us are eager to get rid of any potential problems right away. However, our eagerness to act without conducting proper research is what makes fake antivirus software so successful.
Once you click on the phishing link in the popup and enter your credit card details for the “purchase,” the hackers behind this threat now have your financial data to exploit. Not only can they use this data to conduct identity theft, but you’re also left with nothing but malware in return.
How to Protect Yourself From a Fake Antivirus Tool
Unsure if that antivirus app is real or fake? Fear not! Follow these steps to protect yourself from the hackers and their malicious software:
Watch for suspicious links in popup windows
If you see a suspicious message pop up that says you have a virus or are infected with a malware threat, click the “x” in the corner to close it. These messages often contain phishing links that steal your personal data in exchange for malicious cyberthreats.
Use a legitimate malware detection program
If you are concerned that your computer may be infected with a malware threat, run a scan using the legitimate security software or antivirus product you have installed on your device.
What is the Best Antivirus Software for Optimal Security Protection?
Recruit the Best for Reliable Antivirus Protection
When it comes time to choose an antivirus tool, it can be tempting to select a free antivirus solution. However, free antivirus software can come at a price. Free tools simply don’t offer the level of advanced protection that modern technology users need. We require solutions that are as sophisticated as the threats we face, including everything from new strains of malware to identity theft. Additionally, free antivirus software can typically only be used on one device, while the average consumer has about three!
To ensure that your digital life is protected, use a security suite that has your best interest in mind. Ensure that you have comprehensive internet security installed on all your devices, like McAfee® Total Protection™ or McAfee® Live Safe™ service. Our antivirus suite provides protection from online threats across your PC, Mac, tablet, and mobile device. Additionally, it comes with Password Manager to easily secure and manage your passwords by storing, auto-filling, and generating unique passwords. Furthermore, you can use our file shredder, McAfee Shredder, to delete sensitive files completely, ensuring no traces are left behind.
The cybersecurity landscape is constantly changing, which it why you need to recruit a best-in-class security solution like McAfee Total Protection. With robust, comprehensive security in place, your devices will be consistently protected from the latest threats in the ever-evolving cyberspace. With all your devices safe, you can live your online life free from worry.
Follow us to stay updated on all things McAfee and on top of the latest consumer and mobile security threats.
We’re here to make life online safe and enjoyable for everyone.
System Security is a type of rogue security malware, or smitfraud. It is distributed via malicious websites, but also comes bundled with fake video codecs. Given the ubiquity of video content on the web these days, most PC users are used to installing all kinds of codecs needed to play clips or movies.
Unlike many other examples of rogue malware, system security virus is a well-crafted pest. It causes havoc on infected computers.
Here’s a list of symptoms.
1. Task Mananger, Command Prompt, Registry Editor get disabled. For many PC owners, these are the tools to be used in the first place. This particular malware disables many Windows modules.
2. Currently installed antivirus programs may fail to detect the infection, and are taken over by the virus. When it happens, antivirus software becomes useless; it cannot be started.
3. Desktop wallpaper is replaced by scary warnings.
4. Windows Security Center starts displaying fake warnings urging the user to download the cure.
5. System Security virus comes with a scanner to show fake results of present infections.
6. Almost all applications cannot be open showing the warnings “the file xyz is infected”. No installation of security programs is possible due to same very reason.
Here’s a short list of steps to remove system security virus in case of emergency (when you have no a tech person on call).
1. Open My Computer, go to C:Documents and SettingsAll UsersApplication Data and look for a folder with the numeric name (e.g. 11480154). Inside it, there should be two lonely files, one of them with the numeric filename same as the name of the folder. Delete both files and the folder.
2. Restart Windows.
3. Go to Start, Run, type in MSCONFIG and click OK to launch Microsoft Configuration Utility. Navigate to Startup tab and look for the entry with the numeric name. Uncheck the box near it.
4. If there are entries pointing to C:Program Files with “System Security” in the path, remove the checks from those boxes as well.
5. Right-click on My Computer. Go to System Restore. Check the box stating “Turn off System Restore”. Windows will warn you about restore points being deleted. Click OK and restart.
6. Now enable Windows System Restore (by removing the checkmark from the box in #5).
Finally, run a scan with your antivirus or antispyware software (which should be functioning by now) to remove system security entries.
Security Shield is a renewed version of a dangerous malware Security Tool which has been actively infecting computers and has infiltrated tons of them. The new version of it can be found as Security Shield 2012. Classified as rogue anti-spyware, this application poses a huge risk for infected machine because of its fraudulent expectations to steal unaware users’ money. GUI of Security Shield appears to be just like the one of Security Tool, so this program can be predicted to use the same misleading tactics as the previous malware did. To the date (2012.05) Security Shield is one of the longest -lasting rogue threats. Security Shield got small design change during 2011 and added line “Security Shield 2011″ in the bottom of its design. Later on the line was replaced by “Security Shield 2012″.
After the research of Security Shield we found out that this scam installs onto one’s PC through other malware and fake online scanners. It sometimes uses annoying browser hijackers for its distribution that offer installing its unregistered version for free. The fake scanner pages are promoted through Twitter or other social media spam. In some cases, Security Shield might get installed through drive-by downloads or other trojans.
Having infiltrated computer’s system without letting you know, Security Shield makes some useful modifications that will allow it to launch just after computer’s reboot. Besides, it starts blocking you from using other legitimate programs you need, for example:
Security Shield
“cmd.exe” is infected with “Worm.Win32.Autorun.bnb”. Do you want to register your copy and remove all threats now?
As it was mentioned above, Security Shield starts its malicious strategy as soon as computer becomes active and does that through fake alerts and scanners. However, all these cyber threats reported by malware shouldn’t make you scared – just after getting on board it drops a number of harmless files which later detects as viruses. Do not delete these files, announced by this scam as malicious ones – some of them may be completely harmless and very important files of your system! You should ignore alerts of Security Shield and remove this program as soon as possible. Here are the alerts displayed by Security Shield:
Security Shield
Security Shield Firewall Alert
Security Shield has prevented a program from accessing the internet.
“iexplore.exe” is infected “Trojan-Dropper.Win32.Agent”. This worm has to tried to use “iexplore.exe” to connect to remove host and send your credit card information
Security Shield Warning
Spyware.IEMonster activity detected. This form of spyware attempts to steal passwords from Internet Explorer, Mozilla Firefox, Outlook and other commonly used programs. Click here to immediately remove it with Security Shield.
Security Shield Warning
Intercepting malicious software that may violate your privacy and harm your computer has been detected. Click here to remove now with Security Shield.
Security Shield Warning
Some of the important system files on your PC were modified by malicious software. It may cause system crashes and data losses.
Click here to prevent non-authorized changes and remove threats (Recommended)
Consequently, victims of Security Shield are recommended to register its paid full version which is a huge mistake. As you should have already understood, Security Shield and its alerts are fabricated and must not be trusted. Please, do not follow the tips prompted by this scam because you will make your computer infected even more. The shortest known way to save your machine is to use a reputable anti-spyware and remove Security Shield. Please, do this as soon as possible!
Note: In most cases you CAN download executables, like on your PC directly by entering their url in address bar, for example or Spyhunter installer has malware killing capabilities that work with Security Shield.
If malware remover download is blocked, use following video to overcome Security Shield :
Note!! When removing Security Shield, you can try using this code of registration. It worked with its predecessors Security Tool and System Tool in the past, and malware researcher Siri uncovered that it works with current version of this malware.
64C665BE-4DE7-423B-A6B6-BC0172B25DF2. The code might not work with all versions of Security Shield. The virus should be disabled, so you will be able to run a full system scan with Spyhunter or malwarebytes anti-spywares. You would have much less chances to be infected if you had decent internet security program ( made by Symantec, AVG, ESET, Kaspersky, PCTools), or firewall and decent anti-malware program with real time protection like Spyhunter or Malwarebytes Anti-Malware.
Security Shield 2011 – a fresh version of the rogue
A new version of Security Shield rogue was released that displays 2011 or 2012 in its name aka Security Shield 2011 or Security Shield 2012. It works the same: the rogue application is installed by trojans from video files, shareware or updates. Once Security Shield is installed, you will start seeing lots of alerts that try to scare you. These alerts will claim that your PC is heavily infected and requires a scan, or that a hacking attempt is disabled by Security Shield. Your regular antivirus will be disabled and in many cases it can not be reactivated, thus many users might fall for this scareware trick and do a system scan with Security Shield 2012. The scan will detect various infections, however all detections are fake. First, you will note that the Type and Name of detection will not match: an adware or rogue is detected as a virus. Also, the file location is not displayed in full. If you search for the files detected by Security Shield, you will see that there are no such files on the disk.
Security Shield 2012 is generally the same parasite as Security Shield and belongs to the same malware makers so the code above should work. Do not forget to scan your PC with anti-malware tools afterwards!. We recommend Malwarebytes Anti-Malware, spyhunter and Spyhunter for that.
Automatic Malware removal tools
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
Recommended Posts
Recently Browsing 0 members
- No registered users viewing this page.
- Existing user? Sign In
- Sign Up
Browse
- Back
- Forums
- Guidelines
- Staff
- Online Users
- Members
Activity
- Back
- All Activity
- My Activity Streams
- Unread Content
- Content I Started
- Search
- Back
- Home
- Malwarebytes for Windows
- Malwarebytes for Mac
- Malwarebytes Privacy
Business
- Back
- Business
- Endpoint Security
- Endpoint Protection
- Incident Response
- Endpoint Protection & Incident Response
Mobile
- Back
- Mobile
- Malwarebytes for Android
- Malwarebytes for iOS
Partners
- Back
- Partners
- Malwarebytes Techbench
- MSP
Learn
- Back
- Learn
Start here
- Back
- VPN
- Antivirus
- Malware
- Android Antivirus
- Mac Antivirus
- Hacker
- Cybersecurity
- Identity Theft
- Password Manager
Type of malware/attacks
- Back
- Ransomware
- Keylogger
- Adware
- Spyware
- SQL Injection
- DDoS
- Cryptojacking
- Data Breach
- Computer Virus
- Social Engineering
How does it get on my computer?
- Back
- Malvertising
- Emotet
- Trojan
- Exploit
- Backdoor
Scams and grifts
- Back
- Scam Call
- Spam
- Phishing
- Spoofing
- Create New.
Important Information
This site uses cookies – We have placed cookies on your device to help make this website better. You can adjust your cookie settings, otherwise we’ll assume you’re okay to continue.
1. What is Malware Defense?
Malware Defense is unreliable computer security tool, that crams system with wide range of warning messages also known as false alarms, which are finally used against user for the sole purpose – cash benefits. Affected by such programs (misleading applications), inexperienced and frightened users usually selects inappropriate way to solve computer problems, especially when the issue is security related. Malware Defense is related to Paladin Antivirus, comparing the similarity between the programs.
Malware Defense is carried through Trojan. Also system reboots can be experienced right after Trojan infection, which may develop into reboot loop.
Just before the emergence of Malware Defense, user is noticed that the threats had been found in his system and Malware Defense is recommended as anti-spyware tool to remove them. The alert is imitated as genuine Windows warning through faked Windows Security Center:
Acting on the message, Malware Defense will come up and start computer scan, followed by a prompt Registration required , which will tell that dangerous viruses has been found and removal is necessary as soon as possible.
Viruses found in Malware Defense scan report will indicate legal Windows files ( clock.avi ) or the ones dropped by the program itself.
Security Center Alerts will appear one after another which state that these viruses has been found, asking if user wants them to be blocked:
- Backdoor.Win32.Kbot.al | This Trojan provides a remote malicious user with access to the victim machine. It is a Windows PE EXE file. It is 12787 bytes in size.
- Trojan.Win32.Agent.dcc | This Trojan has a malicious payload. It is a Windows PE EXE file. It is 20480 bytes in size.
- Virus.Win32.Gpcode.ak | This malicious program encrypts files on the victim machine. It is a Windows PE EXE file 8030, bytes in size.
- Net-Worm.Win32.DipNet.d | DipNet.d infects computers running under Windows. The worm itself is a Windows PE EXE file approximately 91KB in size, packed using UPX. The unpacked file is approximately 246KB in size. The worm propagates by exploiting a vulnerability in Microsoft Windows LSASS (MS04-011).
- Rootkit.Win32.Agent.pp | This Trojan masks its presence in the system from users and from other programs. It is a Windows PE SYS file. It is 40960 bytes in size. It is not packed in any way. It is written in C.
- Virus.Win32.Hala.a | This malicious program infects executable files on the victim machine. It is a Windows DLL file. The malicious file is 20480 bytes in size. It is not packed in any way. It is written in Visual C++.
What to do if internet connection has been lost?
- Launch Internet Explorer
- Go to Tools and then Internet Options
- Choose Connections tab
- Click on Lan settings
- Uncheck box next to Use a proxy server for your LAN
- Click OK to close current window
- Click OK to close Internet Options window
2. Malware Defense screen shot:
3. How to remove Malware Defense:
- Internet connection might be disabled or Internet browser might be blocked by Malware Defense, so it won’t be possible to download any files to infected computer. In this case please download all files required for Malware Defense removal to another computer and then transfer them on the infected one using CD/DVD or USB flash drive.
- To remove Malware Defense download Spyware Doctor and install the program (for the installation guide click here). Before installation, make sure all other programs and windows are closed.
- After the installation, computer scan should be started automatically. If so, please move to the next step. If not, click “Status” on the left side menu and press “Scan Now” button to run computer scanner as shown in the picture below:
After the scan has been completed and scan results have been generated, press “Fix Checked” button to remove Malware Defense.
Mr.Peebles
Well recently for no apparent reason our computer got hit with a big virus bomb. One of them is the Sagipsul virus. I had some trouble with this one, constantly popping up new tabs leading to the Sagipsul website that would just be a blank page.
Before that popups for “YOUR COMPUTER IS INFECTED GET A FREE VIRUS SCAN RIGHT NOW”, and “ANTIVIRUS XP 2009” I already realized these were rogue antivirus programs. One day while my sister was using the computer, these popups started to randomly show up while my sister was using firefox. Then it crashed Photoshop. After all the chaos, an icon called, “Gay Fetish Sex” had appeared out of nowhere.
So I did a Malwarebytes full system scan, it showed 27 infected objects, I prompted Malwarebytes to remove them, it said that it removed most of them but not all of them. It stopped the Sagipsul Virus and most of the popups that were popping up. Then everything was fine for a while when something popped up in the side of the taskbar. “Warning! Security report/ Your computer is infected! It is recommended to start spyware cleaner tool.” Currently I’m trying to do a system restore, and when I try and open task manager it says that “Task Manager had been disabled by your administrator.” What?
What is going on?
This is probably a rogue antivirus program.
A trojan fake-alert.
How do I get rid of it?
UPDATE: It looks like the virus just disabled my system restore.
MS Removal Tool is a fake antivirus that impersonates name of legitimate anti-malware tool. The real program is distributed by Microsoft and included in modern Windows OS by default. This is not the first version of malware that uses this name: couple month ago there was another, non related, rogue using Microsoft Malicious software removal tool name. This rogue is far by new, its predecessor System Tool still wrecks havoc on PCs worldwide.
MS Removal Tool infects user PCs through various exploits and trojans. You might get infected when visiting websites displaying infected advertisements or when you download some kind of “free” download from the torrents or web. It is critical to scan all executables downloaded with legitimate antivirus software, or in worst case upload to websites as virustotal.com for double-checking. In other cases your PC will get MS Removal Tool rogue or similar parasite in no time.
After the PC is fully infected, MS Removal Tool will start its advertising campaign to convince you into giving away your credit card details. This malware will replace background with huge warning about infections, and will stop your PC from executing all programs. The malware will display lots of warnings about infections and demand that you launch MS Removal Tool scan and then purchase its full version. This is a trick: There is no full version of this program, and all the files it detect are harmless. However, it is impossible to use PC till MS Removal Tool is removed from PC.
In some cases MS Removal Tool displays various warnings and alerts like these:
MS Removal Tool Warning
Your PC is infected with dangerous viruses. Activate antivirus protection to prevent data loss and avoid the theft of your credit card details.
Click here to activate protection.
Intercepting programs that may compromise your private and harm your system have been detected on your PC.
Click here to remove them immediately with MS Removal Tool.
Security Monitor: WARNING!
Attention: System detected a potential hazard (TrojanSPM/LX) on your computer that may infect executable files. Your private information and PC safety is at risk. To get rid of unwanted spyware and keep your computer safe you need to update your current security software.
CLick Yes to download official intrusion detection system (IDS software).
Warning: Your computer is infected
Windows has detected spyware infection!
Click this message to install the last update of Windows security software…
It also changes the background of Windows desktop and then reports:
Warning!
Your’re in Danger!
Your Computer is infected with Spyware!
All you do with your computer is stored forever in your hard disk. When you visit sites, send emails… All your actions are logged. And it is impossible to remove them with standard tools. Your data is still available for forensics, and in some cases
For your boss, your friends, your wife, your children. Every site you or somebody or even something, like spyware, opened in your browsers, with all the images, and all the downloaded and maybe later removed movies or mp3 songs – ARE STILL THERE and could break your life!
Secure yourself right now!
Removal all spyware from your PC!
Note: Some users make a mistake and pay for MS Removal Tool or similar rogue. In such case you should contact your bank and dispute the charges. Additionally, it is highly advisable to change your credit card numbers, as you might be charged several times later on.
To remove MS Removal Tool, I recommend following procedure:
1. Reboot into safe mode with networking
2. Disable proxy server in your browser.
3. Start task manager and stop processes that look like garbage: random letter and number combo.
4. Download and scan your PC with spyhunter, Malwarebytes Anti-Malware to identify the infected files. Do full system scan or search for stopped processes on the disk.
5. Delete these files.
6. Restore the windows shell to explorer.exe if you haven’t used automatical removal procedure.
In addition, you can try these keys of System Tool infection That still might work with MS Removal Tool as parasites are closely related:
WNDS-TGN15-RFF29-AASDJ-ASD65
WNDS-U94KO-LF4G4-1V8S1-2CRFE
WNDS-6W954-FX65B-41VDF-8G4JI
WNDS-G84H6-S854F-79ZA8-W4ERS
WNDS-TTUYJ-7UO54-G561H-J1D6F
WNDS-A1SDF-6AS4D-RF5RE-79G84
WNDS-A1SDF-RY4E8-7U98D-F1GB2
WNDS-5SRTS-AEHUF-YA54S-D6F35
WNDS-P9685-4H41A-DSW3A-2R64T
WNDS-2AE32-1VFC2-B6894-G67YU
WNDS-4TS8R-D6F5D-4JH8T-U4JK5
WNDS-FGS5D-649RG-4S53D-412SF
WNDS-452S3-ER00F-TSE35-S8FSD
WNDS-SERFH-2642S-F04SD-64FG1
WNDS-F40SA-1ER5H-4FG5D-F8412
WNDS-5D1V2-XB0D5-JT1TY-97DS3
WNDS-4BGY2-JY4KO-IT98Y-7HJ43
WNDS-G8FB6-1V87S-DRT1S-63SRG
WNDS-HFVDR-9844O-U54DA-5TBSC
WNDS-89OF7-7324R-5SAD4-TG68U
WNDS-JUYH3-24GHJ-HGKSH-FKLSD
Full version of Eset Smart Security and most other decent antiviruses, or Spyhunter, Malwarebytes Anti-Malware would have protected from these infections.
Thanks to S!Ri, there have been revealed new registration codes of MS Removal Tool, so try enetering one of them if you have problems with its removal:
WEEA-S0DF5-GS5E0-FG14S-2DF8G
WEEA-JUYH3-24GHJ-HGKSH-FKLSD
WEEA-89OF7-7324R-5SAD4-TG68U
WEEA-HFVDR-9844O-U54DA-5TBSC
WEEA-G8FB6-1V87S-DRT1S-63SRG
WEEA-4BGY2-JY4KO-IT98Y-7HJ43
WEEA-5D1V2-XB0D5-JT1TY-97DS3
WEEA-F40SA-1ER5H-4FG5D-F8412
WEEA-SERFH-2642S-F04SD-64FG1
WEEA-S0DF5-GS5E0-FG14S-2DF8G
WEEA-452S3-ER00F-TSE35-S8FSD
WEEA-FGS5D-649RG-4S53D-412SF
WEEA-4TS8R-D6F5D-4JH8T-U4JK5
WEEA-2AE32-1VFC2-B6894-G67YU
WEEA-P9685-4H41A-DSW3A-2R64T
WEEA-5SRTS-AEHUF-YA54S-D6F35
WEEA-A1SDF-RY4E8-7U98D-F1GB2
WEEA-A1SDF-6AS4D-RF5RE-79G84
WEEA-TTUYJ-7UO54-G561H-J1D6F
WEEA-G84H6-S854F-79ZA8-W4ERS
WEEA-6W954-FX65B-41VDF-8G4JI
WEEA-U94KO-LF4G4-1V8S1-2CRFE
WEEA-TGN15-RFF29-AASDJ-ASD65
Automatic Malware removal tools
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
Having problems with your anti-virus software on Windows?
Learn how to remove the fake virus protector Personal Antivirus! Personal Anti-Virus is NOT a legitimate anit-virus software and will use spyware to steal info from your computer. Personal Anti-Virus is hard to get rid of and is totally annoying. To get rid of it, you don’t have to download anything.
1. My Computer
2. Local Disk C:/
3. Program Files
4. Common Files
5. Un-Install
6. Personal Antivirus Folder
7. Double Click Uninstall
8. Done!
1. CTRL + ALT + DEL
2. Keep it there and go to Local Disk C:/programfiles/(the name of the fake antivirus folder)
3. Look for uninstall button and click it (if none, skip to next step)
4. Task Manager and go to Processes
5. Look for the name of the program on your fake antivirus folder. it should be there. for a certain fake, it will be sb.exe cause thats the name of the program
6. After you find it, press End Process and hurry and go back to your program files and delete all files in the folder FAST before it starts to run again
7. After you deleted the files, there should be nothing in the folder. just go one page back and delete the folder
8. Go to the Recycle Bin and Delete the Files
Want to master Microsoft Excel and take your work-from-home job prospects to the next level? Jump-start your career with our Premium A-to-Z Microsoft Excel Training Bundle from the new Gadget Hacks Shop and get lifetime access to more than 40 hours of Basic to Advanced instruction on functions, formula, tools, and more.
Antivirus Security Pro is a rogue antivirus program that seeks to to get money from users who have no experience with such scams. The program is a member of one of the largest rogue families – WinWebSec. It imitates being a legitimate security application while actually it has no useful functions at all. As it is not expected that anyone would install this program themselves, it is distributed by trojans. Thus it does not require users’ consent to be installed. The program claims that your system is infected and tries to convince you to get a full version of Antivirus Security Pro to remove the infections.
Once your PC is infected, Antivirus Security pro will always be running right from system booting up. It runs a system scan which in a couple of minutes reports about lots of infected items. The scan takes so little time as it only imitates looking for infections and later falsifies scan results. Your computer might be completely fine (besides the rogue itself), but Antivirus Security Pro will claim the opposite.
In addition to a fake scanner, the program displays various security notifications which strengthen the feeling that your system is at risk. These messages appear out of nowhere and report about system errors, spyware and other security related issues. All of them lead to an offer to activate a full version of Antivirus Security Pro. Here are some of the messages that may pop up on your system if you have gotten infected:
Warning! Infected file detected
Location: File System
Suspicious activity detected in the application notepad.exe to the behavior of the virus Win32/Conficker.X. For your security and to avoid loss of data, the operation of application notepad.exe has been temporarily restricted.
Remove Antivirus Security Pro as soon as you detect it on your computer. You should not pay for applications you have not installed yourself and which can not be uninstalled from control panel. If you have other user account available, run antimalware scan, e.g. Spyhunter after logging to it. If you can run a full system scan, this rogue can be removed. This is a very good reason to keep a separate administrator account that is used for such situations only. If this fails, follow the instructions below.
You can also try fake-registering Antivirus Security Pro using this code: AA39754E-715219CE. Remember that it will not remove the program, but only stop its activity for a while so you can run an antispyware and eliminate the application.
Special removal instructions of Antivirus Security Pro
- Reboot, while system boot starts press F8.
- Choose safe mode with networking.
- Start->Run enter . Save file on place you remember. Reboot normally.
- Rename Spyhunter installer from .exe extension to .com extension and run. You will need to be able to see extensions of the known file types. This will restore .exe file associations.
- Install and scan with Spyhunter, Hitman Pro, Malwarebytes Anti-Malware and other anti-malware programs (they should be able to install and run normally now). Delete Antivirus Security Pro startup entries and follow the instructions.
Automatic Malware removal tools
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
Removal guides in other languages
- Antivirus Security Pro (de) Flag of Germany
- Antivirus Security Pro (es)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
2 responses to “ Antivirus Security Pro ”
Antivirus Security Pro also stops me from using safe mode with networking. As soon as I select it, the computer responds with shutting down. I cannot DO ANYTHING. What now?
Michael Schlumpf : Try fake-registering it in normal mode. In some cases this unblocks downloaded programs.
Microsoft Malicious Software Removal Tool is a simple and free utility designed to detect and eliminate malware from the PC. This program scans the system and search for malware presence. If it detects any nasty program, the tool attempts to remove it right away. It works well alongside other antivirus program. However, please remember that Microsoft Malicious Software Removal Tool only scans and detect malware; it was not made to protect the computer against attack.
Even though Microsoft Malicious Software Removal Tool comes packed with Windows update and distribution, you still have to download the most recent version in order to perform efficient scan and removal of viruses. The tool never missed to update its database of malware, thus, it is highly advice to obtain the most recent version before running a scan on the compromised computer.
Microsoft Malicious Software Removal Tool installation is pretty straight forward. It loads like a wizard that guides you through the installation and scan process. We highly suggest performing a full scan if you suspect of malware activities on the PC. Quick mode may be run on regular maintenance basis to ensure that no malware is residing on the computer.
Download and Usage
System Requirements: Windows 7, Windows 8, Windows 8.1, Windows Server 2003 x64 editions, Windows Server 2008, Windows Server 2008 R2, Windows Vista Business 64-bit edition, Windows Vista Enterprise 64-bit edition, Windows Vista Home Basic 64-bit edition, Windows Vista Home Premium 64-bit edition, Windows Vista Ultimate 64-bit edition, Windows XP 64-bit
Disclaimer: By downloading and using this tool, you are considered to have read the owner’s disclaimer and agreed to terms and conditions as declared on the official web site.
2. Once download completes, you can immediately scan the computer by clicking on Run. Alternatively, you can Save the file to the Desktop and perform the scan later.
Feb. 11, 2011 – PRLog — The removal guidelines can be found by clicking this link:
2011/02/security- defender-malware- how-to-delete.html
We would like to tell you about Security Defender. This is the virus and fake anti-malware tool which was introduced by cyber crooks for the only goal– that is to trick you and rob you. Please be on alert and do not trust any fairy-tales Security Defender tells you about.
It should be noted that Security Defender is normally brought to your system by means of certain web sites that present advertisements stating about some “good” online anti-malware scanner. As soon as this advertisement is over it will state that your computer is seriously compromised and then would offer you to download and then later on install Security Defender inside of your machine. We seriously warn you once again that Security Defender is not the program that you should refer to, since it is always installed by means of trojans and other gaps in the system security, and it would make some amendments so that it would be automatically launched with every Windows reboot. As soon as Security Defender is launched it will give all sorts of error messages when you are going to run some applications of your preference or deleting unwanted files from the machine. In order to make your system look as if it is not functioning as well as it must, Security Defender can also cause some folders on your PC show no contents at all. Moreover, Security Defender will prevent some specific applications from regular operation.
To sum up the above-mentioned, if your PC has been compromised with this virus please delete this trash immediately. You should not buy this rogue, because its developers only wanted to fool you and get your money, without suggesting you any decent service at all. This is why you need to follow the advises stipulated below for elimination of Security Defender malware from your computer.
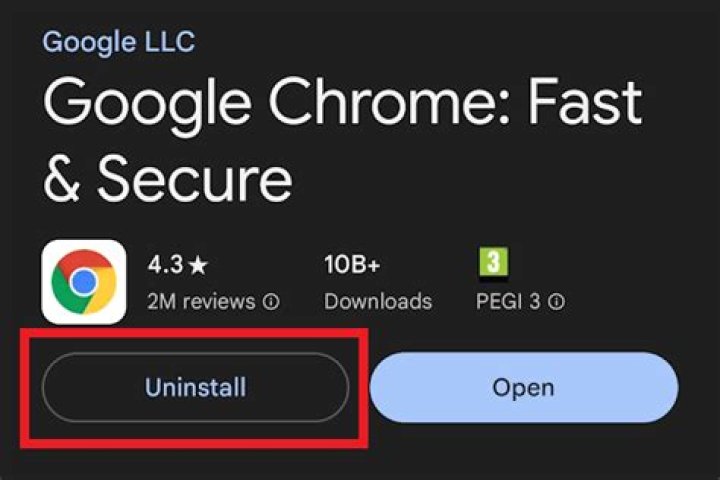
There are many different antivirus programs on the market. If an antivirus is already installed on your computer and you want to install a different antivirus on the computer, you must uninstall the current antivirus program first. Below are the steps on how to uninstall an antivirus program.
Having more than one antivirus program running on a computer at the same time often causes conflicts, resulting in errors, slow performance, and failure to properly detect viruses.
Keep in mind that if you have a subscription with the antivirus company, uninstalling the program may not cancel your subscription.
If you are uninstalling the antivirus because you believe it is causing problems, you can also temporarily disable the antivirus before uninstalling, see: How do I disable my antivirus program in Windows?
Uninstall through the Start menu
First, try utilizing the built-in uninstall feature of the program by finding the folder for the antivirus program in your Windows Start menu. To do this, click Start, All Programs, and look for the antivirus program in the list of programs.
When you find the antivirus program in the list, locate the uninstall option, which should be in the same folder. If this is available, click the uninstall option and follow the prompts to complete the uninstallation of the antivirus.
Uninstall through Add or Remove programs
The second way is to utilize Add or Remove Programs.
Windows Vista, 7, 8, and 10 users
- Open the Add or Remove Programs utility.
- In the list of installed programs, find the antivirus program and select it by clicking it once with the left mouse button. Once the antivirus program is selected, above the column headers, click the Uninstall option as shown in the picture below to initiate the uninstall process.
Some antivirus programs may be listed several times in the list of programs. Make sure you’ve uninstalled all associated parts of the antivirus before rebooting the computer or installing another antivirus.
If you’re unable to uninstall the antivirus through Add or Remove Programs because of an error, skip to uninstalling from Safe Mode. If the antivirus program is not listed in the Add or Remove Programs, you may have a bad antivirus install or a rogue antivirus.
Windows XP users
- Open the Add or Remove Programs.
- In the list of installed programs, find the antivirus program and select it by clicking it once with the left mouse button. To the right of the program name, click the Change/Remove or Uninstall button to initiate the uninstall process.
Some antivirus programs may be listed several times in the list of programs. Make sure you’ve uninstalled all associated parts of the antivirus before rebooting the computer or installing another antivirus.
If you’re unable to uninstall the antivirus through Add or Remove Programs because of an error, skip to uninstalling from Safe Mode. If the antivirus program is not listed in the Add or Remove Programs, you may have a bad antivirus install or a rogue antivirus.
Uninstalling from Safe Mode
In some cases, the uninstall process may not be able to proceed because the antivirus program is currently loaded and running in Windows. If the program cannot be disabled, uninstall the antivirus in Windows Safe Mode. In Safe Mode, the antivirus program is not loaded and running, making it possible to uninstall using either method mentioned earlier.
Bad antivirus program
In some situations, a legitimate antivirus program cannot uninstall because it or the software used to uninstall it is corrupt, bad, or missing. In these situations, you must download an uninstaller program from the antivirus scanner company to remove all files associated with the antivirus. Below is a list of known uninstall links for many of the major antivirus scanner companies.
| Antivirus | Uninstall Link |
|---|---|
| Avast | Avast uninstall link. |
| AVG | AVG uninstall link. |
| Avira | Avira uninstall link. |
| BitDefender 2015 | BitDefender uninstall link. |
| BullGuard | BullGuard uninstall link. |
| Comodo | Comodo uninstall link. |
| Dr. Web | Dr. Web uninstall link. |
| eScan | eScan uninstall link (direct download). |
| ESET | ESET uninstall link. |
| F-Secure | F-Secure uninstall link. |
| G Data | G Data uninstall link. |
| Kaspersky | Kaspersky uninstall link. |
| LavaSoft (Ad-Aware) | LavaSoft uninstall link. |
| McAfee | McAfee uninstaller (direct download). |
| Norton Antivirus Norton Internet Security Norton Security Scan | Norton Antivirus uninstaller (direct download). |
| Panda | Panda uninstaller (direct download). |
| Panda Cloud Internet Protection | Panda Cloud uninstaller (direct download). |
| Sophos | Sophos uninstall link. |
| Trend Micro | Trend Micro uninstall link. |
| Vipre | Vipre uninstall link. |
| Webroot | Webroot uninstall link. |
| Windows Live OneCare | Windows Live uninstaller (direct download). |
| Windows Security Essentials | MSE uninstall link. |
| ZoneAlarm | ZoneAlarm uninstall forum link. |
Rogue antivirus programs
There is also the possibility that the antivirus program attempting to be uninstalled is actually a spyware or malware. There are fake antivirus programs on the Internet and they can do harm to a computer or help someone steal your information. One of the better-known ones to have plagued many computer users is called AntiVirus 2011.
If your computer is infected malware programs posing as an antivirus program, it is strongly recommended that they be uninstalled. You should run a spyware removal program such as Malwarebytes to clean your computer of any other possible spyware or malware programs.
After the arrival of Windows 8 – latest Windows operating system, Windows 8 fake antivirus has been surfaced and spreading around the Windows 8 platform. Normally we call this fake Windows 8 antivirus as a rogue virus application, which harmful malware thread for personal computer.
However, Trend Micro antivirus company has been identifying this fake Windows 8 antivirus threat, calling as TROJ.FAKEAV.EHM. This fake Windows 8 antivirus software produces a rogue security antivirus software warning scan result showing the user’s Windows device being infected with numerous malware, not realizing that the result itself was a form of malware. Meanwhile, the fake antivirus is informing the computer owners need to register for a complete version of the program to have the threats removed, which is false message information and it doesn’t solve the problem totally.
If you’re infected with this fake Windows 8 antivirus, you can remove it by using fake antivirus program remover or use famous antivirus like AVG Antivirus or Trend Micro to remove this fake antivirus. Below is the some of steps to remove fake Windows 8 antivirus:
- Antivirus & Anti-Malware Software – Scan, detect, and remove malware
- System Restore – Restore computer to date and time before Win 8 Antivirus infection
- Uninstall/Manually Remove Fake Antivirus Software – Common guidelines
- Safe Mode With Networking – Troubleshoot internet access, remove malware
Conclusion:
Actually this fake Windows 8 antivirus can be avoidable, user must keep their cool and think twice before clicking links or visiting webpages, especially those that promise the latest items or programs for free. If it’s too good to be true – it probably is.
We can protect ourselves against this rogue application by using real antivirus (like Microsoft, Avast, AVG, SuperAntiSpyware or Malwarebytes), or use an operating system to protect us by other methods (like SmartScreen, present in Windows 8 ). Although the most effective, of course, is common sense and not to download any program that put us ahead .
The 12 Best Linux Distributions for Windows Users
How to Turn Fast Startup On or Off in Windows 10 & 11
How to View Devices by Connection in Device Manager
Here Are All the Device Manager Error Codes and Solutions
Show Your Support for MajorGeeks a Donation
5 Ways to Open Administrative Tools in Windows 10 & 11
How to Create a Safely Remove Hardware Shortcut in Windows 10 & 11
How to Play Minecraft Classic For Free
How to Check Your Available VRAM in Windows 10 & 11
Should You Clean Your Windows Registry?
| -= advertisement =- |
Trend Micro Fake Antivirus (FakeAV) Removal Tool helps you remove and delete fake antivirus applications. Fake Antivirus (FakeAV) threats have been rampant in the past few years. This download is the executable. If your infection is not allowing you to run executables, please see the description for 2 different versions of the tool to work around that issue.
One reason why FAKEAV infections have become well-known to users is because they have visual payloads. Variants of the malware family often display pop-up messages telling users that their machines have been infected. This may cause panic among users, pressuring them to purchase rogue antivirus applications in the hope of resolving the issue. Users, however, should never purchase antivirus software from unknown sources.
Solution:
To help clean the FakeAV infection, download the FakeAV Removal Tool. This tool is still in the beta stage.
Before running the tool, please note the following:
To use the tool, please do the following:
1. Some fake AVs will attempt to block the tool’s execution, so you can choose to download one of the following packages:
Package A: svchost.exe – Use this if the Fake AV blocks extraction of ZIP files. Most users will want this. Note: There is no need to extract the package.
Package B: svchost.zip – Use this if the Fake AV block executables only and there are no other user interactions. Download and extract the package.
Package C: FakeAV Removal Tool – Use this for Fake AV variants that do not block any user execution. Download and extract the package.
2. Run the executable file. If you downloaded either Package A or Package B, the executable file will be named “svchost.exe”. For package C, the executable file will be named “FakeAVremover.exe”.
Note: If you are using Windows Vista/7, right-click on the tool and choose Run as administrator to make sure that the application is not blocked from running.
3. Accept the license agreement.
4. Go to the Settings tab.
5. Click Update Now.
6. Go to the Scan tab.
7. Run a scan by clicking Scan All Processes.
To provide feedback or report issues, do either of the following:
The solution above helps you remove and delete fake antivirus applications such as the following:
Have you seen a pop-up that says “Important notice. Your device is currently infected with a Trojan virus!”?
Webpages made to look like Apple trojan alerts are being used to trick people into installing junk applications.
These “Trojan virus” pages are designed to look like security alerts delivered by Apple, although Apple never shows alerts like these.
The “Remove Virus” button shown by the alerts leads to a page on the App Store, pushing you to install a promoted app. The alerts falsely imply that the app is an Apple-endorsed antivirus solution. Often, these apps have relatively high subscription fees, that people might be intimidated into paying.
Fake Alerts Your Device Is Currently Infected With A Trojan Virus quicklinks
- What the false alert looks like
- Scammers impersonate Apple
- They threaten your data
- They offer a fake solution
- How to avoid fake virus detections and other malicious ads
- How to remove malicious apps
- Automatic Malware removal tools
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
About the “Your device is currently infected with a Trojan virus!” alert:
it says that your device is infected with “a Trojan virus”,
it recommends an app to “Remove Virus”,
close suspicious webpages without interacting with them,
What the false alert looks like
You may have encountered alerts saying that your device is infected with a Trojan virus (“Your device is currently infected with a Trojan virus!”) and you have to install an app to solve it. These alerts are nothing more than scams. Scammers collect app subscription payments from people who fell for the fake warning.
The malicious alert might show up while you’re browsing the web. It might also come as a notification from your calendar, browser, or another app.
Here’s what the “Your device is currently infected with a Trojan virus!” warning looks like (or at least one version of it).
Important notice. Your device is currently infected with a Trojan virus!
Your phone’s memory is already having 17% of damage.
Prompt action is required, otherwise,
the device will become defective and all your data
including accounts, photos, and payment data will be
available to third parties.
Immediately install the trusted free app from the AppStore to remove the virus and secure your device.
Scammers impersonate Apple
It claims to be from Apple Security. It is not, but it’s trivial for malicious actors (or anyone, really) to create a webpage that looks convincingly like another company’s webpage. The URL of the alert is certainly not Apple.com, but again, it’s simple for malicious actors to make it look somewhat believable, like “Applecomsupport.com” or “Apple.com-optimizing-mac.live”.
Impersonating another site is called spoofing (sometimes also phishing).
They threaten your data
The alert says that your device is infected and that it’s being increasingly damaged right now. It also threatens that your data will be leaked to third parties. There might be a timer at the bottom counting down seconds to, presumably, something very bad happening.
Scammers like to create a sense of urgency in order to discourage people from looking for help or getting a second opinion.
They offer a fake solution
The alert then offers a way to “remove the virus” by installing the “trusted free app”. Click the Remove button and an App Store page opens.
The apps pushed by the fake Trojan alert tend to be various VPN and antivirus apps. They also tend to have dozens of glowing reviews, so they might look “trusted” at first glance. However, if you look into their terms of service and home sites, you might notice that these apps are developed by mostly unknown third-party companies and definitely not Apple.
The apps are also not free, despite what the “Your device is currently infected with a Trojan virus!” alert promised; they usually cost at least a few dollars a week, up to a hundred per year.
How to avoid fake virus detections and other malicious ads
Apple’s devices are pretty safe from malware, but not from scams. Scams such as the fake Trojan alert don’t rely on novel programming tricks or security exploits; they just use psychological tricks to scam people.
So, if fake Trojan virus alerts are not a technical problem, how do you solve it?
First, you can use an ad blocker. Not on all sites – most mainstream sites don’t show ads that would lead you to fake trojan alerts. But if you visit pirating sites, free movie sites, video converter sites, etc., then it’s pretty much mandatory to use an ad blocker.
Adware infections, such as bad browser extensions, can also cause malicious advertisements to show up on your screen. If there’s adware on your device, it needs to be removed.
You can also use other tools, like malicious site blockers and anti-malware programs with real-time web security.
But it’s impossible for security tools to catch all malicious websites. So, when you come across a suspicious alert, take a screenshot and post it on a community forum, such as Discussions.apple.com. It’s good to ask for a second and third opinion about these things.
“Your device is currently infected with a Trojan virus!” is not the only fake virus alert that preys on Mac and iPhone users: there are alerts like 27 viruses, 3 viruses, Apple Security Alert pop-ups, and many others.
How to remove malicious apps
To find and delete adware infections, malicious and suspicious apps, and protect your device from malware, it’s helpful to use an anti-malware app like Malwarebytes, Combo Cleaner, Spyhunter for Mac. and others.
If you come across an ad like the “Your device is currently infected with a Trojan virus!” alert, close it without downloading anything from it. If it’s hard to get rid of the unwanted browser tab, check out our post on the various ways to close webpages.
Automatic Malware removal tools
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
WinThruster software is developed by Solvusoft Corporation, a US-headquartered company. It is advertised as a registry cleaner and a system optimizer. The developers of the program promise that by installing and activating its full version users will be able to improve the functionality of their computers and the systems will function in a faster way.
Winthruster Virus quicklinks
- Is WinThruster worth trying?
- It’s detected by anti-malware programs
- Optimizers and registry cleaners
- How to remove WinThruster
- Automatic Malware removal tools
- How to remove WinThruster virus using Windows Control Panel
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
The fact that WinThruster is the product of Solvusoft Corporation, a Microsoft Gold-certified software development company, probably gives more credibility to the program, however, there are some complaints from the people who installed it. They mentioned that there were no enhancements noticed after they purchased this optimizer and that the performance of their Windows operating system was instead diminished.
WinThruster looks very similar to SlimCleaner, PC Speed Maximizer, Auto System Speedup, and some other programs. Even their interface is basically the same, as well as the functionality and behavior within the system. All these programs ask for the license to be purchased in order to fix the so-called problems allegedly revealed upon completion of their system scans.
Fake optimizers like WinThruster are more likely to slow down your computer than do anything useful. You can feel free to uninstall them:
Remove suspicious programs using anti-malware tools (Malwarebytes).
Cancel your WinThruster subscription.
Is WinThruster worth trying?
It’s detected by anti-malware programs
We scanned WinThruster (WinThruster installers and its executable) with security programs. The scan results showed why you might want to avoid this program. A few of the scanners identified this installer as suspicious: it was marked as a Trojan/Win32.TSGeneric, W32/Trojan.XWVJ-8199, Program.Unwanted.952, Riskware/SlowPCfighter, PUP.Optional.Solvusoft, Artemis!Trojan, PUA.Winthrust.
To be fair, the 2020 version of WinThruster is better than its 2019 version. Here’s a scan result of the current version of WinThruster: Virustotal.com. In addition, the software ethical behavior watchdog AppEsteem has given WinThruster its blessing back in 2017. So, it’s not like WinThruster is malicious. Just kind of potentially unwanted and not as useful as its promotional material implies.
Still, it’s good to be careful of PUPs (potentially unwanted programs), even though they’re not outright dangerous.
Optimizers and registry cleaners
Registry cleaners are often immediately suspicious because, notoriously, Microsoft does not recommend using them.
When it comes to registry-cleaning utilities and system optimizers like WinThruster is that they can make misleading promises and report harmless issues as problems. They then offer to fix these issues that might not really need to be fixed. However, this does not always improve system performance. Outdated or unused registry entries don’t impact system performance in a perceptible way.
WinThruster offers a free-trial version that has limited functionality. It also offers a one-year subscription to the paid service of WinThruster amounts to $39.95 USD.
Generally speaking, the majority of so-called system optimizers are reported to be absolutely useless, since their functionality is very primitive. They may get rid of some outdated components, however, they may as well delete important system files that will result in more complex problems to occur – editing the registry is especially risky. Furthermore, while the free trial period of WinThruster is in place, the program will keep scaring users with the series of faulty alerts claiming that the computer is experiencing problems that allegedly need to be immediately fixed.
This is why antivirus programs detect the WinThruster program as potentially unwanted. It’s important to be aware that a registry cleaner like WinThruster can be helpful in limited circumstances, but it’s far from necessary.
How to remove WinThruster
Some people speak of WinThruster as a virus or rogue security software. However, it is more correct to classify WinThruster as a PUP (potentially unwanted program). This is the way that anti-malware programs detect it. Many antivirus programs ignore WinThruster because it’s not really harmful.
So, if you want to get rid of WinThruster, we recommend you to scan your computer with a powerful anti-malware utility (like Malwarebytes) that can recognize PUPs. It will help to identify all available components of WinThruster within the system and to delete them effectively.
You can also remove WinThruster manually by accessing the Control Panel of your computer, locating it in the list of available programs, and deleting it. Or you can use Windows settings, Apps & features to remove it.
It might be first necessary to end the task of the program in the Task Manager.
Automatic Malware removal tools
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to remove WinThruster virus using Windows Control Panel
Removal guides in other languages
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How Did the Rogue Security Software Install Itself on My Computer?
Some of the infections may have come from you downloading an infected codec file when you were trying to watch a video online, like the Zlob trojan, or opening an infected PDF file. Malicous flash or java programs can also infect your computer with these rogue security software programs.
Finally browser exploits, security issues in the browser, can allow some of these infections to install themselves.
How Can I Protect Myself
There are a number of things you can do to protect your computer from becoming infected with a rogue security application.
- Keep your Computer up-to-date with Windows Updates
- Keep your Antivirus, AntiSpyware, and Firewall Applications up-to-date
- Be careful when clicking on links in email or on social networking sites
- Be aware of phishing scams and how to avoid them. Phishing scams are generally emails wanting you to go to a web page and enter personal information about your bank, credit card, or other private information that can be used in identity theft. No legitimate organization will ever instruct you to go to a web site and enter this info. If you have a question, stop and call the organization directly about the email.
- Use a limited user account instead of an administrator account when surfing the net. Limited account will not allow you to install programs without asking for your permission and a password first.
Step by Step Directions for Removing Rogue Security Software Programs
Listed below you will find various pages on how to remove these fake spyware cleaner programs. Not every rogue security program is listed here, because most can be removed using a standard removal procedure in Windows Safe Mode with MalwareBytes AntiMalware.
Recommended Posts
Recently Browsing 0 members
- No registered users viewing this page.
- Existing user? Sign In
- Sign Up
Browse
- Back
- Forums
- Guidelines
- Staff
- Online Users
- Members
Activity
- Back
- All Activity
- My Activity Streams
- Unread Content
- Content I Started
- Search
- Back
- Home
- Malwarebytes for Windows
- Malwarebytes for Mac
- Malwarebytes Privacy
Business
- Back
- Business
- Endpoint Security
- Endpoint Protection
- Incident Response
- Endpoint Protection & Incident Response
Mobile
- Back
- Mobile
- Malwarebytes for Android
- Malwarebytes for iOS
Partners
- Back
- Partners
- Malwarebytes Techbench
- MSP
Learn
- Back
- Learn
Start here
- Back
- VPN
- Antivirus
- Malware
- Android Antivirus
- Mac Antivirus
- Hacker
- Cybersecurity
- Identity Theft
- Password Manager
Type of malware/attacks
- Back
- Ransomware
- Keylogger
- Adware
- Spyware
- SQL Injection
- DDoS
- Cryptojacking
- Data Breach
- Computer Virus
- Social Engineering
How does it get on my computer?
- Back
- Malvertising
- Emotet
- Trojan
- Exploit
- Backdoor
Scams and grifts
- Back
- Scam Call
- Spam
- Phishing
- Spoofing
- Create New.
Important Information
This site uses cookies – We have placed cookies on your device to help make this website better. You can adjust your cookie settings, otherwise we’ll assume you’re okay to continue.
Recommended Posts
Recently Browsing 0 members
- No registered users viewing this page.
- Existing user? Sign In
- Sign Up
Browse
- Back
- Forums
- Guidelines
- Staff
- Online Users
- Members
Activity
- Back
- All Activity
- My Activity Streams
- Unread Content
- Content I Started
- Search
- Back
- Home
- Malwarebytes for Windows
- Malwarebytes for Mac
- Malwarebytes Privacy
Business
- Back
- Business
- Endpoint Security
- Endpoint Protection
- Incident Response
- Endpoint Protection & Incident Response
Mobile
- Back
- Mobile
- Malwarebytes for Android
- Malwarebytes for iOS
Partners
- Back
- Partners
- Malwarebytes Techbench
- MSP
Learn
- Back
- Learn
Start here
- Back
- VPN
- Antivirus
- Malware
- Android Antivirus
- Mac Antivirus
- Hacker
- Cybersecurity
- Identity Theft
- Password Manager
Type of malware/attacks
- Back
- Ransomware
- Keylogger
- Adware
- Spyware
- SQL Injection
- DDoS
- Cryptojacking
- Data Breach
- Computer Virus
- Social Engineering
How does it get on my computer?
- Back
- Malvertising
- Emotet
- Trojan
- Exploit
- Backdoor
Scams and grifts
- Back
- Scam Call
- Spam
- Phishing
- Spoofing
- Create New.
Important Information
This site uses cookies – We have placed cookies on your device to help make this website better. You can adjust your cookie settings, otherwise we’ll assume you’re okay to continue.
360 Total Security virus Removal Guide
- 360 Total Security – a poor security software
- Advertising and distribution methods of the rough antivirus
- Uninstall 360 Total Security antivirus entirely
- How to prevent from getting system tools
- References
What is 360 Total Security virus?
360 Total Security – a poor security software
360 Total Security is a suspicious antivirus program created by the Chinese company called Qihu 360 Software Co Ltd. This program does not only offers poor protection from cyber threats but might get into the system unnoticed and aggressively urge to obtain the license key too.
| Summary | |
|---|---|
| Name | 360 Total Security |
| Developer | Qihu 360 Software Co Ltd |
| Type | Potentially unwanted program |
| Danger level | Medium. Can get installed unnoticed and bring other unwanted apps to the system |
| Symptoms | Sudden system scans and virus alerts |
| Distribution methods | Official website, third-party download sources, freeware and shareware downloads |
| To uninstall 360 Total Security, install Reimage Intego and run a full system scan | |
So-called 360 Total Security virus is identified as a potentially unwanted program (PUP), [1] and has been actively distributed for a couple of years. Among the most affected users are located in the United States, India, [2] and Egypt. At the moment of writing, it’s compatible with Windows and Mac operating systems.
From the first glimpse, 360 Total Security may seem as a genuine anti-spyware. [3] It claims to be able to detect viruses, Trojans, and other emerging threats. According to the test results, the program does not detect major cyber threats and might provide fake system scan results.
Hence, 360 Total Security might inform about non-existent cyber threats on your computer. This sneaky technique is used to convince you to buy a license key of this questionable program. However, even the paid version of the program does not help to clean computer.
360 Total Security program has an official download website. However, it often sneaks into the system bundled with various free programs. What is worse, it does not arrive on the system alone. It might also bring Bitdefender and Avira engines or other PUPs.
If 360 Total Security manages to infiltrate a computer, it adds a scheduled task to Windows Task Scheduler and launches at certain scheduled times. Besides, it connects to the Internet and adds a Windows Firewall [4] so that a genuine anti-spyware would not block it.
In addition to that, it installs a shortcut on the Internet and continuously runs the executable qhsafemain.exe in Task Manager. It seems that it is responsible for continuously displaying misleading 360 Total Security alerts.
Of course, you can stop these annoying activities. First of all, you have to uninstall 360 Total Security from Windows. However, we have told that it might bring other unwanted apps to the system, so you should find and get rid of all these entries.
If you want to remove 360 Total Security together with its related components manually, you can follow our prepared guide at the end of this article. Keep in mind that attentiveness is needed. Otherwise, you might overlook some of the PUP-related components.
However, if you have problems with 360 Total Security removal or want to speed up the procedure, you should opt for automatic elimination method. You have to obtain a professional anti-malware software, such as Reimage Intego , and run a full system scan.
360 Total Security alerts might annoy you after secret installation of a questionable security software.
Advertising and distribution methods of the rough antivirus
Despite the fact that this suspicious security tool has an official download website; this tool might sneak into the system using other techniques. Authors of the program might use the following methods to promote and install a program on as many computers as possible:
- fake update alerts, [5]
- fake online scanners,
- malicious links
- freeware or shareware downloads.
Users are most likely to experience 360 Total Security hijack when they download free programs carelessly. If you rely on Standard/Recommended installation settings, you should ditch this habit right now! It’s the main way how PUPs enter the machine.
These settings do not openly disclose what additional apps might be included in the same package as a free program. Hence, all of the entries get into the system silently without asking user’s permission. Fortunately, you can switch to Advanced/Custom setup and avoid this unpleasant situation.
Additionally, it is recommended to stay away from security alerts popping up on the screen while browsing the web or trying free online scanners to check if your device is not infected. Such ads are typically malicious.
Uninstall 360 Total Security antivirus entirely
We have briefly mentioned two possible ways to remove 360 Total Security from Windows OS. If you are willing to get rid of the program and its related components manually, follow these steps:
- Click Start and select Control Panel.
- Click Uninstall a Program under Programs.
- Choose 360 Total Security and select the Uninstall/Change option.
- Click Yes and OK to save the changes.
Additionally, you should check your web browsers from unknown extensions or search engines. This tool is known for installing Bitdefender and Avira engines. We highly suggest terminating these tools because they might have features of the browser hijackers. You can find more information on how to fix your browsers below. Additionally, you can opt for automatic 360 Total Security removal.
You may remove virus damage with a help of Reimage Intego . SpyHunter 5 Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.